Connectors & Cybersecurity: Interconnect Solutions Help Protect Digital Assets
Data breaches are a billion-dollar problem, wreaking havoc with financial systems, medical records, businesses, and individuals. As supply chains and infrastructure also become increasingly connected, protecting cybersecurity is critical. Strategic hardware selection can help protect networks.

Cybersecurity is often portrayed as a white hat hacker at a monitor, scanning code in search of vulnerabilities in networks. But thwarting malicious actors and protecting data integrity is a complex effort that involves multiple people and multilayered approaches. Software solutions, policies that define how data is handled, training personnel to identify phishing and other scams, enhanced building security, and physical hardware from verified sources that has been designed with security in mind all play a role in protecting digital assets.
Electronic connectors aid in cybersecurity
Electronic connectors, used in conjunction with other components or software, can help perform encryption, authentication, access control, and intrusion detection functions. On a basic level, a smart card with an electronic connector can authenticate and admit access to a computer system or a physical entry point to a secure building. such as a data center. Similarly, a secure communication channel between two devices can be established by encrypting the data passed through an electronic connector. In high-stakes environments such as government or military operations, designers must specify the highest quality of interconnects.
“Cybersecurity functions are embedded throughout a large share of modern military hardware systems. This includes not only data centers and C5ISR systems, but UAVs, weapon systems, and other manned and unmanned military vehicles,” said Joel Wetsig, business development analyst at Amphenol Aerospace. VPX (VITA 46) connectors and rectangular connectors used throughout military cybersecurity hardware to provide high-speed data transfer and power connections between boards within a system, he said.
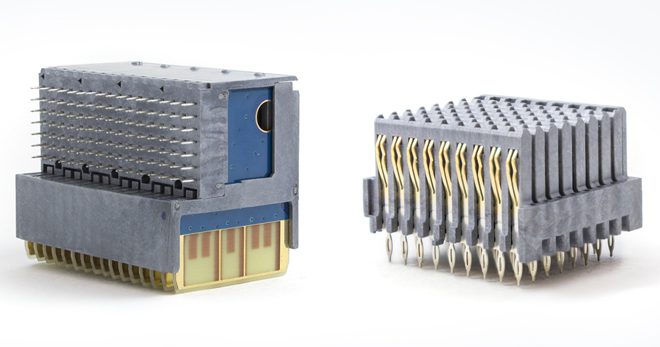
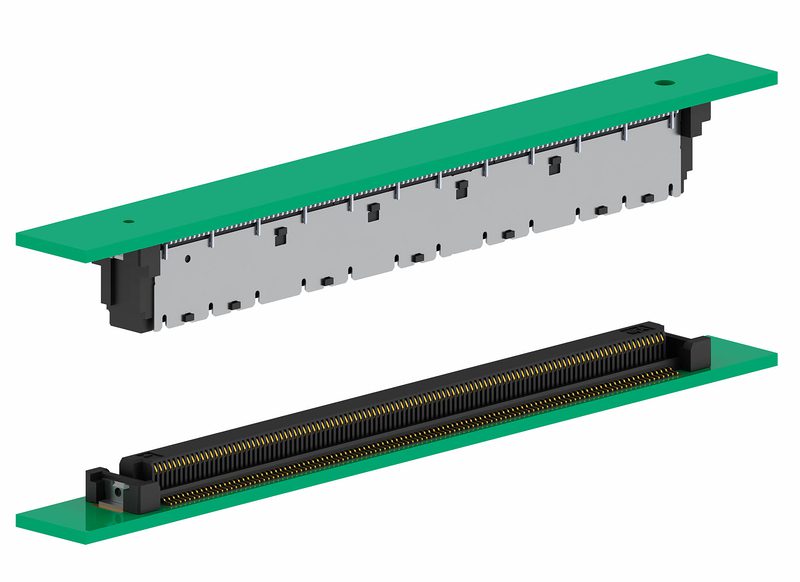
Amphenol’s new MIL-HD2 VITA 91 interconnect adheres to the Open Group Sensor Open Systems Architecture (SOSA) technical standard. Designed to achieve 56 GB PAM4 data rate requirements with higher density, this connector was designed for use in embedded computing applications such as commercial and military aerospace, C4ISR electronic systems, missile defense, ground systems, space systems, and other ruggedized environments.
They are designed to withstand harsh conditions such as vibration, shock, and extreme temperatures and are highly secure against signal interference and tampering. These interconnects connect boards that handle sensitive information and critical systems, such as those involved in communications, navigation, and command and control applications. Cybersecurity is a critical concern for military operations, including:
- Network security: Protecting military networks and systems from unauthorized access, intrusion, and data extraction.
- Cyber defense: Identifying and combating cyber threats, such as malware and Advanced Persistent Threats (APTs), in real-time.
- Information assurance: Ensuring the confidentiality, integrity, and availability of critical military information.
- Electronic warfare: Using cyber capabilities to disrupt, deceive, or degrade the enemy’s ability to use the electromagnetic spectrum.
“VPX and board-level rectangular connectors utilized in these applications must be ruggedized, durable, reliable, and lightweight while providing industry-leading data transfer speeds and EMI protection,” said Wetsig. “And as the U.S. military, intelligence community, and allies continue to pivot back toward geopolitical rivals in Europe and Asia that may have similar capabilities as ours, these systems will only become more relevant.”
Point of sale security
In military and other critical infrastructure systems, human lives can be made vulnerable by cyberattacks. But financial assets are a key target for many hackers. Point-of-Sale (POS) terminals. Credit card numbers and PIN codes are temporarily stored on POS terminals. This data can be accessed by attackers using probes or mini-drills. HARTING developed the 3D-MID to provide an additional hardware security element.

HARTING’s 3D-MID is a protective cap for POS systems, which helps mechanically and electronically protect the electronics inside the device from unauthorized access. A high-precision meandering structure detects even the smallest intrusion, thus preventing data theft.
Moving that data more quickly also helps reduce the time it is stored in a device. ept Connectors’ Colibri highspeed connectors are ideally suited for high data transfer rates and can be used in COM Express and Mezzanine board-to-board systems with data transfer rates for 10 Gigabit Ethernet and PCI Express Gen3. A new version available later in 2023 will feature 25+ Gb/s speeds and has been designed for AI and other high-speed technologies.
Secure Cables’ Role in Cybersecurity
Secure cables also play a critical role in cybersecurity efforts. As data moves through cables, it can be intercepted by unauthorized parties. Cables can be vulnerable to physical attacks in which it is cut or tapped, and data is intercepted or malicious devices are installed which give access the network. Faulty or damaged cables can cause data loss or network downtime, which can be exploited by attackers. Physical security measures, such as cable locks or conduits, protect cables from physical tampering and the use of high-quality cables — along with regular preventative maintenance — help protect critical networks, including data centers, financial systems, research centers, government facilities, and military operations.
Connector companies collaborate with software providers
Increasingly, hardware and software providers are working in concert to bolster cybersecurity efforts for their shared customers. Interconnect companies are collaborating with software firms to integrate data analysis in the design of secure network architectures. Phoenix Contact Group recently acquired Canadian company iS5 Communications Inc., a provider of services and solutions for critical infrastructure networks. As the company continues to prioritize industrial automation, IoT technologies, and other connected solutions, protecting those networks becomes an essential part of system design. Martin Müller, Vice President of Phoenix Contact, said, “The expertise of iS5 Communications Inc. enables Phoenix Contact to take a leading position in the market for critical infrastructure networks and to further expand the business together.”

Phoenix Contact’s industrial routers connect various networks via cable (LAN router and NAT router) or mobile network (2G/3G/4G/5G) for remote maintenance and protection. A large number of products feature integrated VPN and firewall functions. For the highest level of security, the mGuard routers protect against cyber attacks and malware.
Würth Elektronik is partnering with Crypto Quantique, a specialist in quantum-based cybersecurity in the Internet of Things (IoT). “Expanding the offering with QuarkLink makes implementing and managing secure IoT networks faster and easier,” said Dr. Shahram Mossayebi, CEO of Crypto Quantique. “At a time when the global threats to such networks are greater than ever, this is an important advantage.”
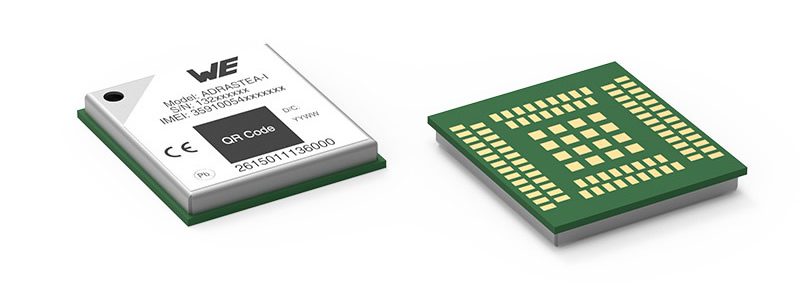
Würth Elektronik’s wireless modules support connectivity via Bluetooth, Wi-Fi, Wireless M-Bus, Wirepas Mesh and proprietary radio protocols. Cellular connectivity sends generated data direct to internet. This generated data is transmitted with security, authenticity, and integrity through end-to-end encryption and advanced client authentication.
As electromechanical components, connectors and cables are only parts of a larger cybersecurity strategy that includes software and human intelligence. But as data breaches become more prevalent and devastating, designers of connected systems must take every measure to harden systems by selecting hardware designed for secure performance.
Like this article? Check out our other networking articles, our Datacom Market Page, and our 2023 and 2022 Article Archive.
Subscribe to our weekly e-newsletters, follow us on LinkedIn, Twitter, and Facebook, and check out our eBook archives for more applicable, expert-informed connectivity content.
- Building New Connectivity Products with Safer Substrates - June 2, 2026
- What is an Elastomeric Connector? - May 26, 2026
- Nurses Help Influence Interconnect Design - May 19, 2026